Really giving a jot about JWTs
Instacart Sr Security Engineer David Gillman (or Gilman? Either OWASP or LASCON got it wrong) presented a talk in 2021 and followed up with a podcast interview released today.
One thing David is excellent at describing developer benefits, and developer-centric Patterns and Anti-Patterns when using JWT. If you are an enthusiast of JWT this is really interesting. But what if you are a security professional who really is just a stakeholder of the JWT? (you want to be informed of security outcomes your peers have implemented) then you really just want to know the security characteristics of the solution.
David unfortunately misses a massive fundamental characteristic of JWT throughout his discussion on the podcast, and that lack of knowledge was even more noticeable in the slides; Verifying a JWT = the JWT is well-formed and not modified since it was signed. verifying a JWT is not granting authorisation, and verifying certainly is not the same security characteristic as validation.
David very clearly intermixes the concept of verify and validate to the determent of the entire message, no distinction was made of how the JWT verification is done by JWT framework (or library) because it has the ability to operate on the JWT itself and needs no context of the organisation solution, whereas validation is never possible outside your organisation and therefore you never get validation methods in JWT frameworks - i.e. you must always verify the claims are well-formed using the library and then write your own solution to validate the claim data itself before it is used.
The example of Authorisation:
embedding a role in a token
Firstly, that is an ACL mechanism - you are not talking about Authorisation at all.
We would all agree OWASP is authoritative source on what Authorisation is, and is not. So as a contributor myself to the OWASP Cheat Sheet Series where I clarified several distinctions and example of what exactly Authorisation is leading up to the OWASP Top 10 2021 release where A01:2021-Broken Access Control took the number one position - I would claim to be one of few who can with certainty that everything described are examples of a small portion of what makes up an ACL solution, and none of that small portion where JWT fits has any description of Authorisation in any way.
An aside: I wonder if this distinction (lacking a definition of Authorisation) is what led to also using verify and validate interchangeably? Perhaps..
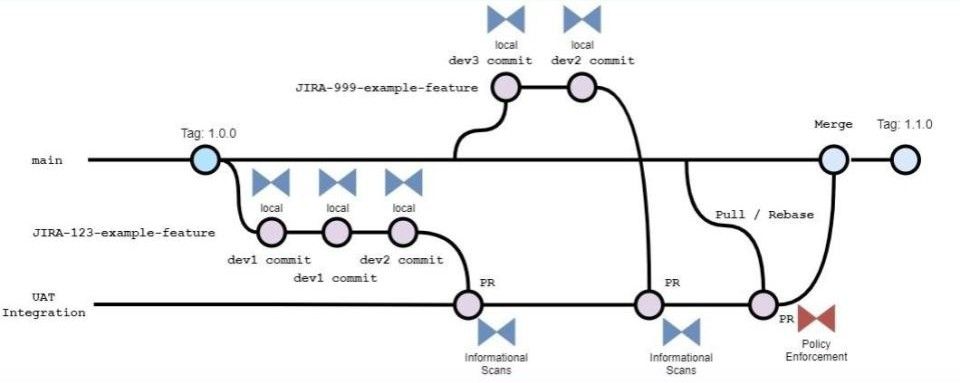
Watch this space for a follow up post on JWT Patterns that provide real security benefits



Member discussion